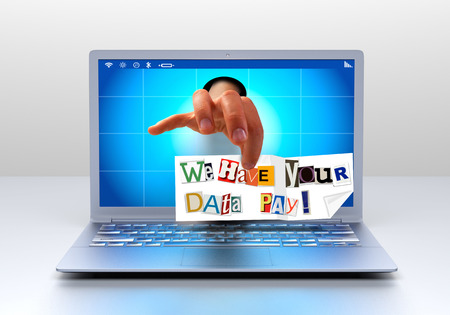
If you have been watching any of the news feeds in the technology fields or even business magazines, you will be well aware that hacking, ransomware and other computer threats have taken over headlines.
You might be wandering why this problem is growing more prevalent, and if there is a chance that you might get caught up by it. Sad to say, the answer is yes and there are a couple of reasons why:
- It’s easy money for the scammers. Because they set up a fake site and collect payment in bitcoins, it is hard to trace back to them.
- The bad guys have matured and gotten much, much shrewder. No longer is it just some kid in his parent’s basement.
No, now it has evolved into a high tech, multi-million-dollar industry.
The methodology behind the growing threats
The big players have created their own “products” and just like you might franchise or license a product you created, they do the same. It’s like when you purchase a subscription to Office 365, or Co-Schedule or Dropbox, the developers of malware/exploit programs are using this model, too. They build it once and then sell it over and over to their “clients.”
The clients use it to victimize their targets and then the developer takes a cut off the top of what is collected. It’s a business model that has been in place for a very long time and, I have to say, it works.
According to an FBI tally, ransomware attacks cost their victims a total of $209 million in the first three months of 2016, and the numbers are not expected to drop anytime soon.
How do you protect yourself and your business?
Awareness of the threat is just the first, albeit critical, step. Knowing what to do to protect your network from being a target of all these computer threats is the next one. The following are the best two suggestions to fight the battle:
- Backup, Backup, Backup! This is the fastest, easiest, and probably least expensive way to restore your data should you be hit. But remember, it is for AFTER you get hacked. Although that is the case, it is the best way to prevent someone victimizing you in a ransom scam.
- Prevention-wise, the name of the game now is layers. The bad guys are coming at you from all angles, not just the old school virus way in which they infect your site to corrupt your data or systems or crash it completely. In the past when dealing with viruses and the like, a simple anti-virus software would protect you. Although that must remain as a still necessary part of the prevention plan, you also now need an anti-exploit and zero-day way to stop/prevent these new computer threats from happening in the first place.
So what is an “anti-exploit and zero-day way”?
The best way to explain is to tell you about a new Techno-Advantage partnership with a company called Sophos.
Sophos is an industry leader in security for small- and medium-sized businesses. They offer an assortment of products that all work and talk with each other.
For example, if one of your workstations gets infected, the Sophos product installed in it sends a signal out to a firewall blocking all traffic to/from the machine until the exploit is contained. It also notifies the network that problem has been “isolated” or “quarantined,” which means the rest of the network is safe.
They even produce software that detects if ransomware is encrypting files on your computer and stops it, then actually reverses the encryption.
The goal is to flag you and kill the process before it has a chance to corrupt your whole computer or any of the files on a server drive.
It’s really impressive how everything “talks” together to provide several layers of protection for your computer and network.
Several other companies offer different versions of malware/anti-exploit software as well, and we have used several of them. Most of them will offer a trial, or a free version. However, we have found that many of them are not ongoing. By that I mean that it is not software that is continuously scanning, but just a manual scan to remove malware after your computer is infected. And you can guess that that is not going to reverse the encryption from a ransomware attack. If that happens, hopefully you have that backup current and handy.
The bottom line is that as technology advances, so do the bad guys and the computer threats they devise. They learn new ways to target and victimize users and now, to make it of monetary benefit to them.
Be aware and then take the steps you need to in order to protect yourself and your business.